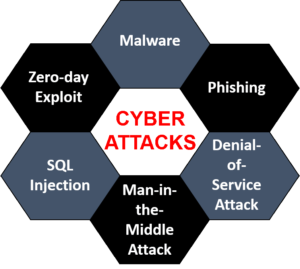
The Six Most Common Cyberattack Types

Do you know The Six Most Common Cyberattack Types? Cyberattacks are the most common attacks worldwide that are caused by people, according to the World Economic Forum Global Risk Survey for 2020.
No matter how big or small, cybercrimes pose an imminent threat to every entity (government, business, and person). It is untrue that only large corporations handle cyber-attacks. Attackers target internet-connected devices as a possible tool to disrupt businesses with less advanced cybersecurity protections. The types of cyberattacks and their techniques have changed over the past few years along with technological advancement.
Read More:Jazz Internet Packages 2021: 3G, 4G Daily, Weekly, and Monthly
Every day, cyberattacks strike businesses, causing enormous losses in productivity, assets, and income as well as damage to a company’s reputation, business confidence, and trust, as well as violations of consumers’ fundamental right to privacy.
The Six Most Common Cyberattack Types
Knowing the fundamentals and origin of cybercrimes before taking security measures will help you identify the problem’s root cause and permanently eradicate it.
What are the most prevalent categories of cyberattacks?
What impact do they have on the company?
Let’s examine the six prevalent cyberattack categories that cause the greatest harm.
1. DDoS
DDoS, or distributed denial of service attacks, occur when a computer system targets a network, server, or other website source and prevents the target’s users from using particular services. As a result, hundreds of notifications, incoming messages, and connection requests cause the target system to sluggish down. DDoS assaults have the potential to completely disrupt and shut down a system, leaving its legitimate users without service.
In the first half of 2020 alone, there were 4.8 million DDoS attacks, showing that every firm deals with this serious issue. Every year that goes by, they record the greatest number of attacks. Ai technologies are used by the attackers to determine what strategies are most effective. Unfortunately, These days, AI is employed to strengthen every cyberattack. You need a comprehensive software solution like XDR [Extended Detection And Response], which combines STEM, endpoint detection and response, and network detection and response, to keep cyber attacks at bay. Such systems offer better visibility, automation, and exact endpoint analytics. You can save time and react swiftly using AI and automated technologies.
2. Malware
A harmful file or intrusive programme created specifically to aid attacks at the expense of consumers is referred to as malware, also known as malicious software. Despite the fact that there are numerous varieties of malware, their fundamental methods are the same. These malware employ sophisticated invasion strategies created in a manner that deceives users and allows for unauthorised device installation. Ransomware, Trojans, and spyware are the three most popular categories of malware.
3. Phishing
Phishing is a type of cyberattack in which the perpetrators pose as well-known organisations, such as banks, email users, tax authorities, etc. Through the use of phoney links or attachments, fraudsters deceive consumers into handing over sensitive information like credit card numbers, passwords, and other intellectual property. Phishing is a simple way to obtain sensitive data. There are various phishing attack types, including:
- email phishing
- angler phishing
- spear phishing
- whaling
4. SQL injection attacks
The vast majority of websites rely on data, making them susceptible to SQL injection attacks. A SQL query used by the attackers to slowly insert malware onto your device. These attacks can serve a variety of purposes; this year, emails were stolen via SQL. Attackers’ malicious requests change and alter the database so that they can readily access sensitive information about your clients or their personal information.
5. XSS
Another type of injection attack called XSS allows attackers to insert harmful data, such as a script from another piece of software. You should be aware that XSS gives an attacker the ability to steal cookies by injecting scripts created in a variety of languages, including JavaScript, Ajax, Java, Flash, etc. By posing as a user, the attackers can simply trick the victims, spread malware, cause mayhem, and access the users’ personal information with ease.
6. Botnets
Although bonnets are distinct from other cyberattacks, the attack method is very similar to phishing attempts. This involves a number of computers or gadgets that cybercriminals are in charge of. The main goals of the attacker are to increase attack intensity and infect as much software as they can.
Conclusion
Even though they may be unavoidable, cyberattacks can be rapidly stopped if they are identified early. These assaults, though, have the potential to permanently corrupt, rob, and destroy data. Therefore, it is essential to implement the proper cyber security measures to prevent them from accessing your systems. Furthermore, you need to put in place a multi-level security system that successfully safeguards your data when criminals opt for sophisticated assaulting methods.











